Underground Weather API Key lays the foundation for seamless underground weather forecasting by providing a structured approach to API key implementation, security, and management.
This comprehensive guide explores the types of API keys, their benefits and limitations, and how they are utilized in various programming languages such as Python, Java, and C++. Moreover, it delves into security and authentication mechanisms, best practices for storing and managing API keys, and designing a secure infrastructure.
Best Practices for Managing and Storing Underground Weather API Keys
Proper management and storage of Underground Weather API keys are essential for securing your data and preventing unauthorized access. API keys can grant access to sensitive information and functionalities, making it a target for malicious activities. Therefore, it’s crucial to handle them with care and follow best practices.
To manage and store API keys effectively, consider the following:
Using Environment Variables
Environment variables are a secure way to store sensitive information, such as API keys, outside of your code. This approach prevents hardcoded keys from being exposed directly in your code or configuration files. Most programming languages provide built-in support for environment variables. To use environment variables, you can set API keys as environment variables on your development or production servers.
Secure Configuration Files
Secure configuration files, like those using a secret key, offer an additional layer of security for storing API keys. These files are encrypted and can only be read with the decryption key. This method ensures that sensitive information, such as API keys, cannot be accessed without the decryption key.
Encrypted Storage
Encrypted storage solutions, like HashiCorp’s Vault or AWS Secrets Manager, provide secure and centralized key management. These tools encrypt and store sensitive information, including API keys, and offer role-based access control, audit logs, and automation features.
Regularly Reviewing and Updating API Keys, Underground weather api key
Regularly reviewing and updating API keys is crucial for ensuring that your API credentials remain secure. Check for expired or deprecated keys, and update your credentials as necessary. Consider implementing a secure key rotation strategy to minimize the impact of API key compromise.
Monitoring for Suspicious Activity or API Key Abuse
Regularly monitor API key usage for signs of suspicious activity or unauthorized access. Implementing logging and alerting mechanisms can help detect and prevent API key abuse. Consider using API key management tools that provide monitoring and alerting features.
Tools and Software for Managing and Secure API Keys
Several tools and software solutions can help manage and secure API keys, including:
- Hashicorp’s Vault: A secure key management store for sensitive data.
- AWS Secrets Manager: A secure and highly scalable service for storing sensitive data such as API keys.
- Kubernetes Secrets: A feature for securely manage sensitive information, such as API keys, in containerized environments.
- API Key Managers: Tools specifically designed to manage and secure API keys, such as AWS API Gateway and Google Cloud API Gateway.
By following these best practices and utilizing the available tools and software solutions, you can ensure the secure management and storage of Underground Weather API keys.
Closing Summary: Underground Weather Api Key
By understanding the intricacies of Underground Weather API Keys, individuals and organizations can streamline their API key management, ensuring seamless integration with weather forecasting systems and minimizing security risks.
Remember to stay vigilant and adapt to evolving security landscapes to maximize the effectiveness of Underground Weather API Key in your system.
FAQ Compilation
What is the primary benefit of using API keys in underground weather forecasting?
API keys provide a secure layer of authentication, enabling reliable data exchange between applications and weather forecasting systems.
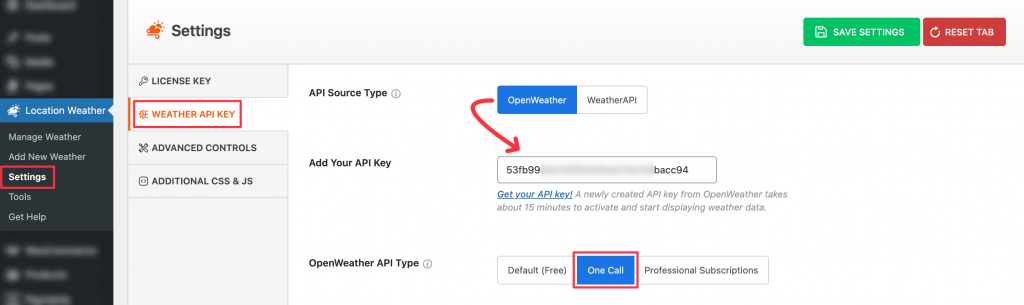
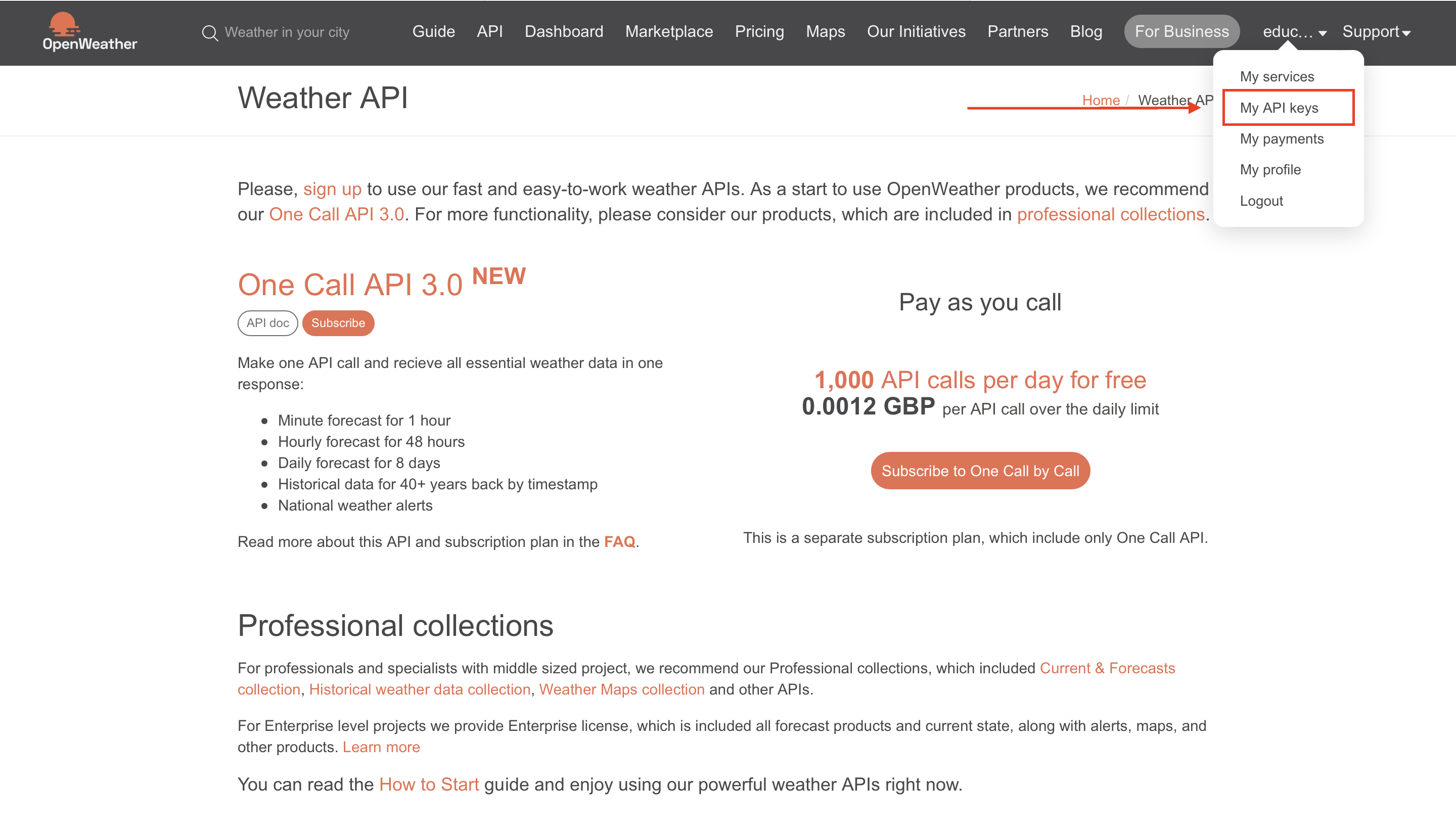
How can I ensure the secure storage of my API keys?
Store your API keys in secure configuration files, environment variables, or encrypted storage to prevent unauthorized access.
What are some best practices for managing my API keys?
Regularly review and update API keys, use load balancers and caching for scalability and performance, and monitor for suspicious activity or API key abuse.
Can API keys be compromised, and how can I prevent data breaches?
Yes, API keys can be compromised. Implement robust authentication and authorization mechanisms, such as OAuth 2.0, API keys with HMAC, or token-based authentication, to prevent data breaches.